The digital world is surrounded by cyber-attacks, which require well-trained cyber warriors who can spot, detect, and restrict threats. There is a great need for knowledgeable cyber security professionals, far exceeding the supply available, providing exciting opportunities for individuals to land a new role in the cyber space.
The Cybersecurity labor crunch is also expected to hit 3.5 million unfilled jobs by the end of 2023, and the number of open positions is expected to triple. Therefore, cybersecurity professionals have a lot of career opportunities right now.
Are you knowledgeable enough to keep up with the demands of industry? We’ve compiled 12 common questions (and their answers) regarding the cyber space that you must know in order to land your next job.
1. Cybersecurity: What does it mean?
The term “cybersecurity” refers to the protection of hardware, software, and data against attacks. Protecting sensitive information from cyberattacks such as accessing, changing, or destroying it is the primary purpose of cyber security.
2. What is the difference between Threat, Vulnerability, and Risk?
Threat: Any risk that carries the ability to obstruct operations, steal data, or otherwise cause harm is considered a threat.
Vulnerability: This term describes flaws in a system that increase the likelihood and hazard of threat outcomes.
Risk: This term describes a triad of threat probability, impact, and loss. In plain terms, it has to do with the potential harm or loss that could result from a danger exploiting the weakness.

Risk = Threat Probability x Potential Loss
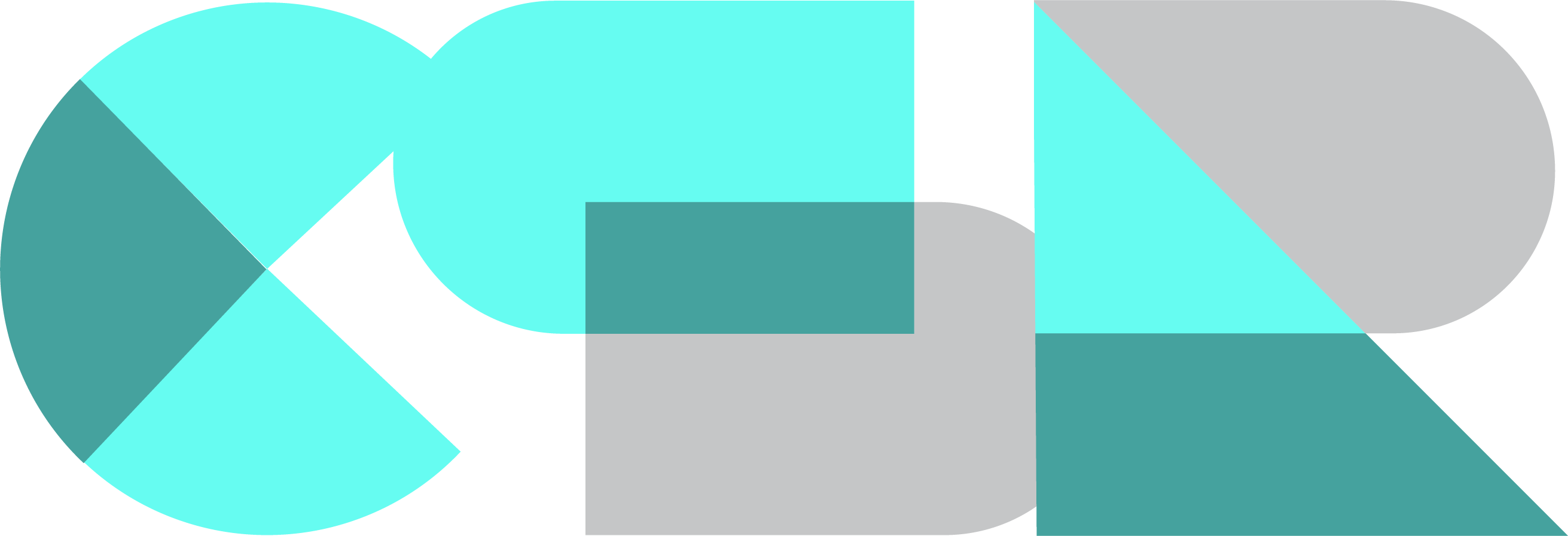
3. What are the typical forms of cyber security attacks?
Cyberattacks have a number of harmful consequences. When an attack is conducted, it may result in data breaches, which may cause data loss or manipulation.
The frequency of cyberattacks has significantly increased during the COVID-19 pandemic, according to Interpol and WHO. Today’s globe is subject to a wide range of cyber threats.
Let’s look at the various types of cyberattacks on our list
4. What is a Firewall? What is it used for? What are four common types of Firewalls? How can it be implemented?
A firewall acts as a barrier between a local area network and the Internet. It keeps private resources private while reducing security risks. It manages network traffic both inbound and outbound. Firewalls, which can be implemented as hardware, software, or both, are typically your first line of defense against malware, viruses, and attackers attempting to gain access to your organization’s internal network and systems. Firewall inspects each data packet before allowing it in, much like a walk-through metal detector door at a building’s main entrance. It looks for the source and destination addresses and determines whether or not a data packet should pass through based on predefined rules.
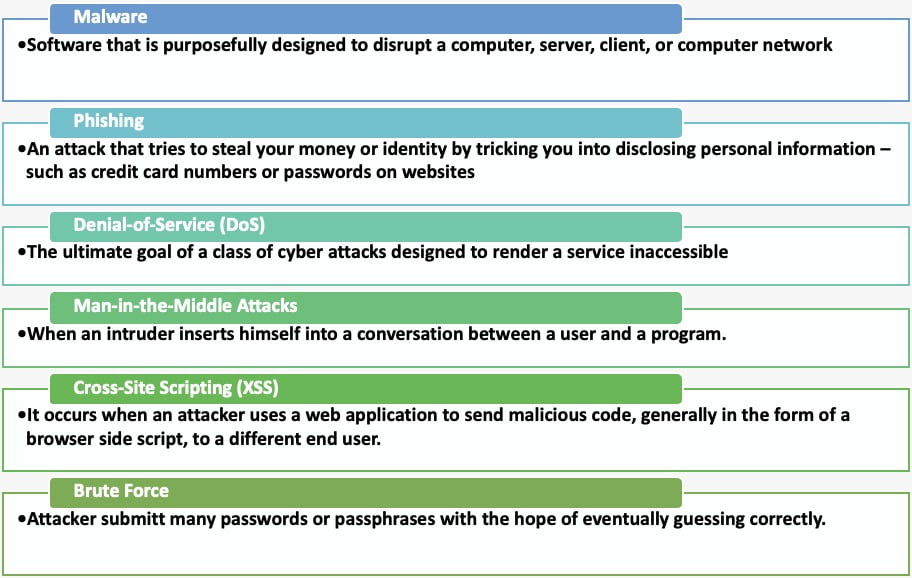
Firewalls are also classified according to how they operate, and each type can be configured as either software or a physical device. Firewalls are classified into four types based on how they operate.
1- Packet Filtering Firewalls: They operate at the network layer, examining a data packet’s source and destination IP addresses, protocol and destination ports, and other details against pre-established rules to decide whether to pass or discard it. They monitor each packet independently and are fast, cheap, and effective. However, the security they offer is quite minimal.
2- Circuit-Level Gateways: Transmission Control Protocol (TCP) circuit-level gateways confirm established connections and keep track of ongoing sessions. They primarily assess the safety of an established link. They are inexpensive, straightforward, and barely affect the performance of a network. However, they are an insufficient security solution on their own because they cannot examine the data packets’ contents.
3. Stateful Inspection Firewalls: Often referred to as dynamic packet filtering, is a firewall technology that keeps track of the status of active connections and makes decisions about which network packets to let pass through the firewall based on this data.
4. Application-Level Gateways (Proxy Firewalls): It is a form of security software or hardware that shields the servers and apps from potentially dangerous data. It combines upper layer functionality with lower layer access control, as well as having a proxy agent that mediates communication between two hosts. Proxy firewalls perform stateful and deep packet inspection.
How is Firewall implemented? The following is a list of the steps necessary to install and configure the firewall:
● A firewall device’s default password should be changed.
● Turn off the remote administration function.
● For particular programs to work properly, such as an FTP server or a web server, set up port forwarding.
● If a firewall’s DHCP is not disabled, installing a firewall on a network with an active DHCP server may result in issues.
● Ensure that the firewall is set up with strong security policies.
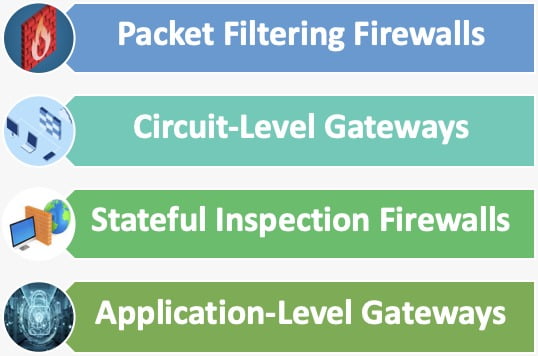
5. What distinguishes penetration testing from vulnerability assessment?
Penetration testing may be included in a vulnerability assessment, but they are separate processes. The purpose of vulnerability assessments is to identify weaknesses, whereas penetration tests are intended to show how well cyber defenses work. The purpose of a vulnerability scan is to identify and report potential vulnerabilities in an automated, high-level way. But during a penetration test, your system is thoroughly examined by a real person to detect and exploit weaknesses.
6. How can two-factor authentication be implemented on public websites?
❖ Dual-factor authentication or two-step verification involves the user providing two authentication factors in order to protect both credentials and resources.
❖ Public services like Twitter, Microsoft, LinkedIn, and others can use two-factor authentication to provide another layer of security to accounts that are already password-protected.
❖ You may quickly access settings and then modify security settings to enable this twofactor authentication.
7. What is Cross-Site Scripting and how can it be prevented?
An attack known as Cross-Site Scripting, or XSS, involves injecting malicious code into the web browser of the victim to execute malicious scripts.
Cross-Site Scripting can be prevented by the following procedures:
❖ Encoding special characters
❖ Using XSS HTML Filter
❖ Validating user inputs
❖ Using Anti-XSS services/tools
8. What is a Botnet?
A set of internet-connected devices, such as servers, PCs, mobile phones, etc., that are compromised by malware and under its control is known as a botnet.
Data theft, spam distribution, distributed denial-of-service (DDoS) assaults, and other activities are possible with it. It also gives the user access to the device and its connection.
9. What is a CIA triad?
An organization’s information security rules are handled using the CIA (confidentiality, integrity, and availability) triad approach.
❖ Confidentiality(C) – A collection of rules that limits access to information.
❖ Integrity(I) – It assures the information is trustworthy and reliable.
❖ Availability(A) – It provides reliable access to data for authorized people.
10. What is RDP, or Remote Desktop Protocol?
The Microsoft RDP (Remote Desktop Protocol) protocol was created with the goal of securing and encrypting application data transfers between client devices, users, and a virtual network server. It enables administrators to assess and address problems faced by specific subscribers from a distance. With a facility for multipoint transmission, it supports up to 64,000 different data channels.
11. What is a three-way handshake?
In a TCP/IP network, the process of establishing a connection between a host and a client is known as a three-way handshake. Due to the three-step process used by the client and server to exchange packets, it is known as a three-way handshake.
These are the three steps:
❖ The client sends a SYN(Synchronize) packet to the server to see if it is online and whether any ports are open.
❖ If the client has open ports, the server will send a SYN-ACK message to it.
❖ This is acknowledged by the client, which then returns an ACK(Acknowledgment) packet to the server.
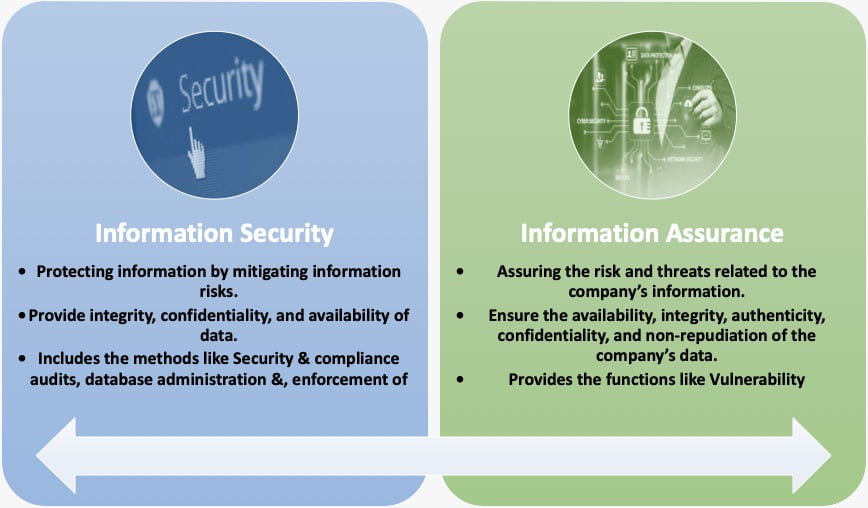
12. What distinguishes information assurance from information protection?
Information security/protection prevents unauthorized access to the data through encryption, security software, etc. whereas Information assurance maintains the data’s dependability by guaranteeing confidentiality, availability, and other factors.
The only area of IT that has not experienced a recession is cyber security. Demand brings competition, so you have to be among the best to land a job in cybersecurity. While possessing the required cybersecurity abilities is the first step, passing the interview is a completely different story. We’ve put together this collection of the best Cyber Security interview questions and answers to assist you ace the test.
And Remember, both certification and skills are important Best of luck !